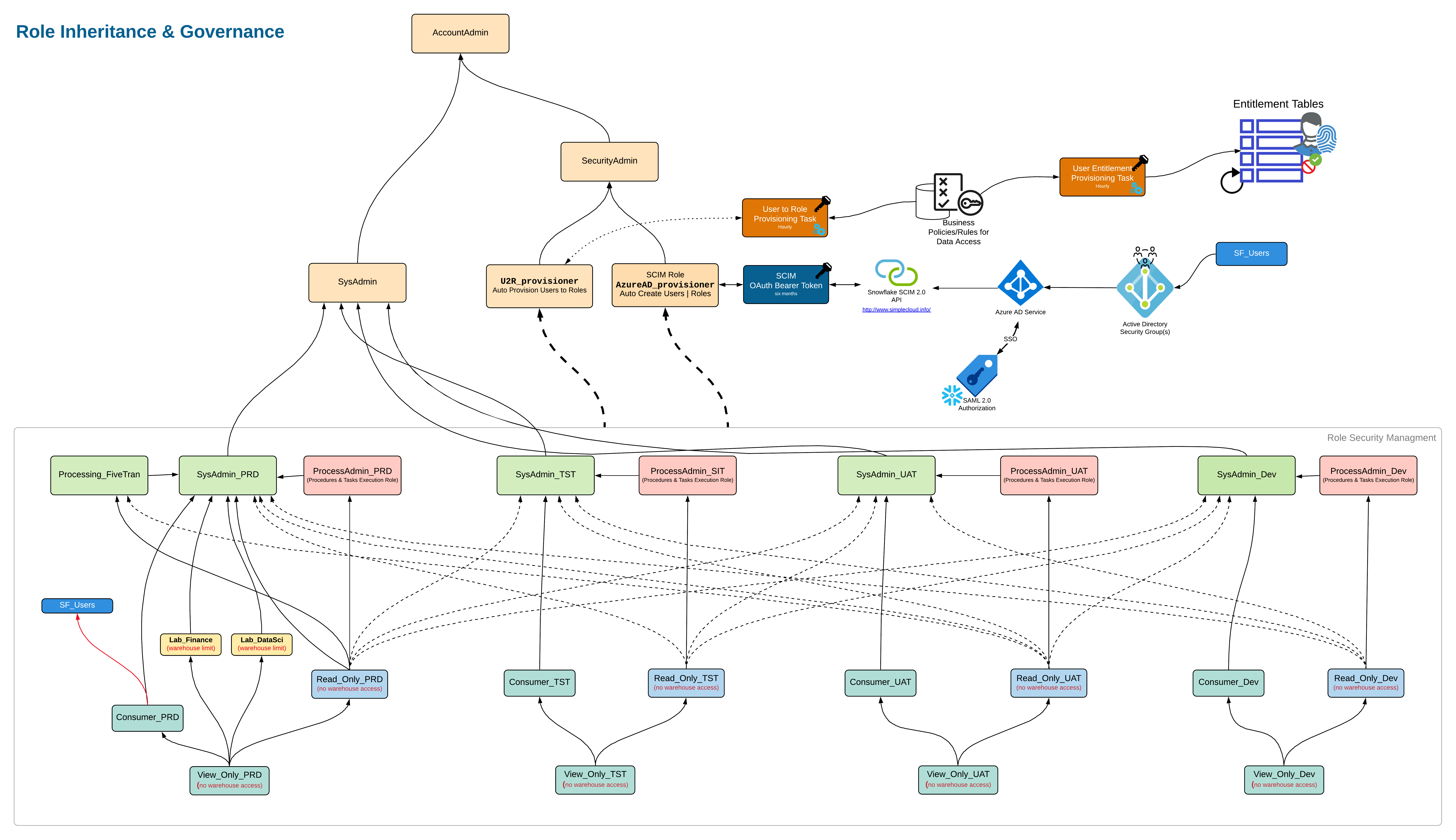
The power of Snowflake is it's ability to scale without a fuss. No hardware, no performance degradation, no locking, and no storage limitations. No wonder why organizations are moving to Snowflake. However, there is a catch, Snowflake's unlimited data estate requires Administrators to adapt to an inheritance up model. The Access Control Master delivers an adaptation to this model to combine roles.
See the Access Control Master in Action
In this recorded session FlowObjects does a deep dive on into the typical security architecture in Snowflake, and how the Access Control Master modifies this pattern to deliver the security inheritance that most organizations are accustomed to. Additionally, FlowObjects will demonstrate how the Access Control Master simplifies the management of your objects and roles.
"FlowObjects Access Control Master tames one of the most challenging barriers to broad Snowflake adoption."

Base Access Control
The Base Access Control delivers a Master script that can restore tables, schemas, stored procedures, streams, shares, functions, snowpipes, to the correct ownership and access control.
-
Object Naming Conventions
Defined best practice naming convention to enable downstream automation for each layer of the Snowflake environment
-
Base Role Definitions
Defined base roles customized to your development lifecycle which will be used in object creation and ownership
-
Master Script
Based on the Naming Conventions and Role Definitions, the master script lays down all the foundational security and structure.
-
Master Script Extensibility
The Master Script provides a single location to add new databases and schemas which the master script will enforce the defined security. This also ensures the appropriate ownership of objects.
-
Master Reset to Standards
Master Script will automatically fix, tables, schemas, stored procedures, streams, shares, functions, snowpipes, etc to the correct ownership and access control.
Advanced Access Control
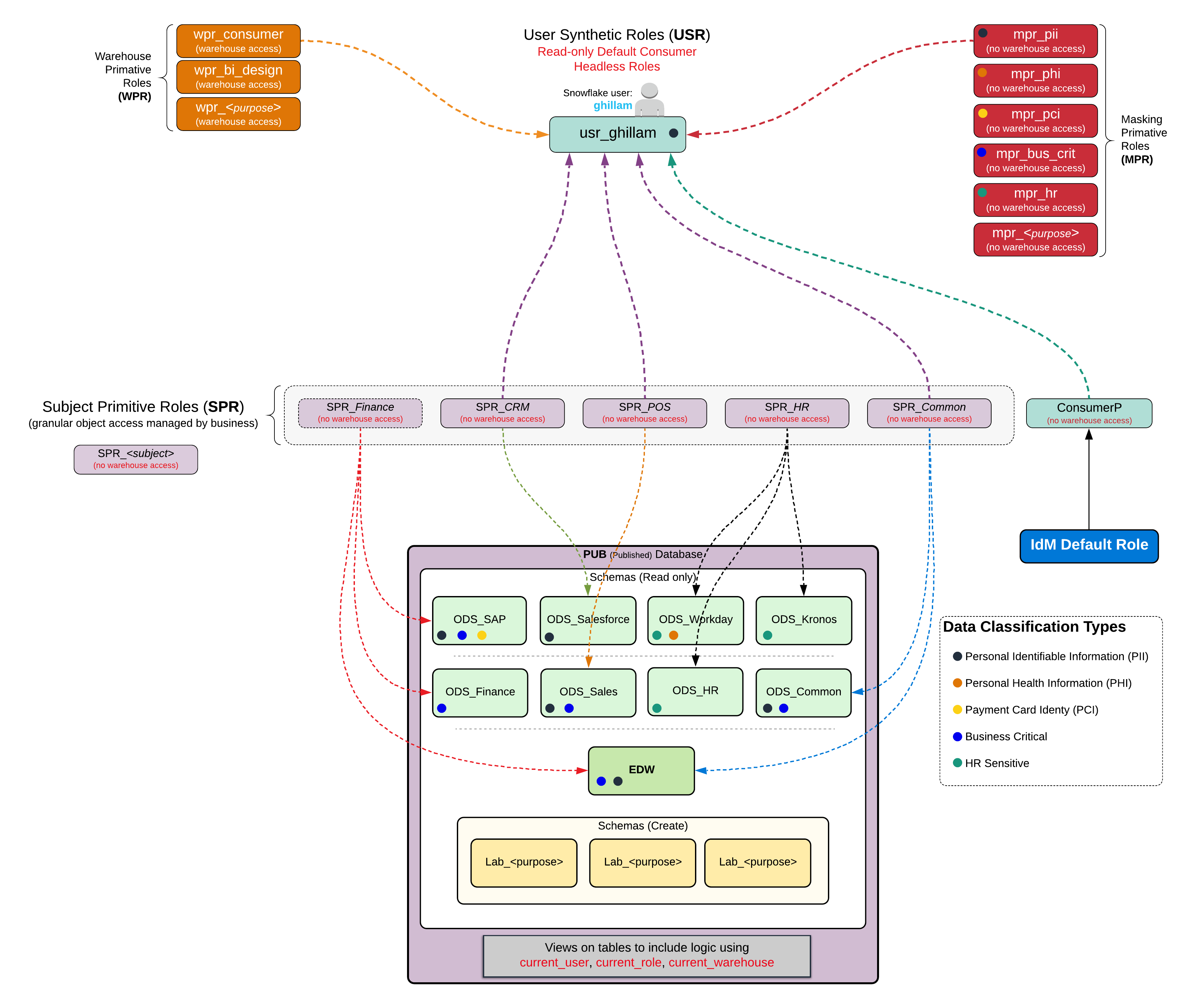
All the features of Base Access Control plus added features to focus on the users of data. This provides granular access control for the users, while simplifying administration and the end user experience.
-
Tie to External Definitions
Advanced Access Control can integrate with multiple Identity Management Systems, HR Systems, and other identification sources all at once.
-
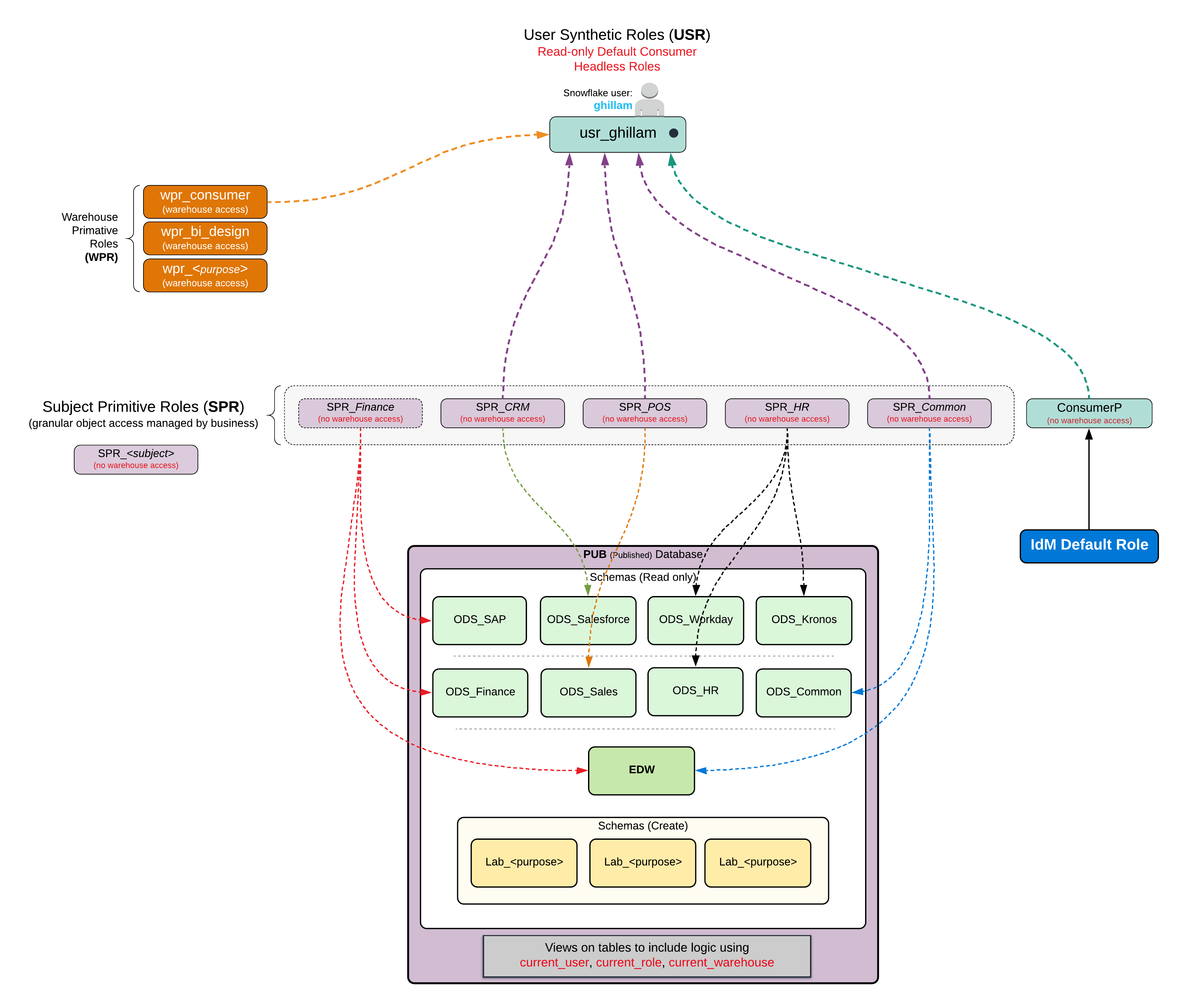
Enabling the Creation of Granular Data Segments
Create Access Controls for discrete data sets that are subject oriented called Subject Primitive Roles.
-
Tie Data Segments to Users
Allocate the data segments to users in either an automated or manual process. This allows external Identity Management solutions to drive data access.
-
Create Specialized User Roles
Specialized roles in Snowflake are created for each user's individual roles. These roles get assigned to the data segments defined which is called a User Synthetic Role. This acts as a proxy for the user enabling inheritance from Subject Primitive Roles.
-
Automation of Associations
With the Advanced Access Control in place the organization can deal with the ebbs and flows of employee promotions, hiring, role changes, and requests for access, via your current identity management solutions. This means that the business users can be the arbiters of who has access to the data.
Advanced Access Control + Sensitive Data
Everything in Advanced Access Control plus the ability to mask sensitive data based on classifications at the table/column level.
-
Classify Sensitive Data in Snowflake
Classify your sensitive data so that it is identified in your data estate.
-
Apply Data Masking Policy for the Classification
For each classification there will be a masking policy implemented, as well as a masking role.
-
Associate Users to Masking Policies
Tie the User Synthetic Roles to the Masking Primitive Roles which will allow defined users to see the data unmasked.
Base
Per Snowflake Instance
Object Governance
Master Script
month
year
Deployment Services
Fee
Per Snowflake Instance
Object Governance
Master Script
month
month
Deployment Services
Fee
Advanced
Snowflake Instance
Everything in Base
Granular User Access Control
month
year
Deployment Services
Fee
Per Snowflake Instance
Everything in Base
Granular Advanced Access Control
month
month
Deployment Services
Fee
Advance + Sensitive Data
Snowflake Instance
Everything in Advanced
Data Masking
month
year
Deployment Services
Fee
Snowflake Instance
Everything in Advanced
Data Masking
month
month
Deployment Services
Fee